A cross-site scripting vulnerability has been reported by the WPScan Vulnerability Database. The vulnerability was discovered by RipsTech security software company on October 25, 2018. It is unclear whether the vulnerability has been patched.
UPDATED:
All in One SEO Pack Updated their Changelog
Sometime after this article was published, All in One SEO Pack updated their changelog. Now, the changelog is clearer that a security patch was issued on December 6, 2018.
Here is a tweet from December 16, 2018 noting that the changelog was updated:
 Here is a screenshot of the new version of the changelog:
Here is a screenshot of the new version of the changelog:
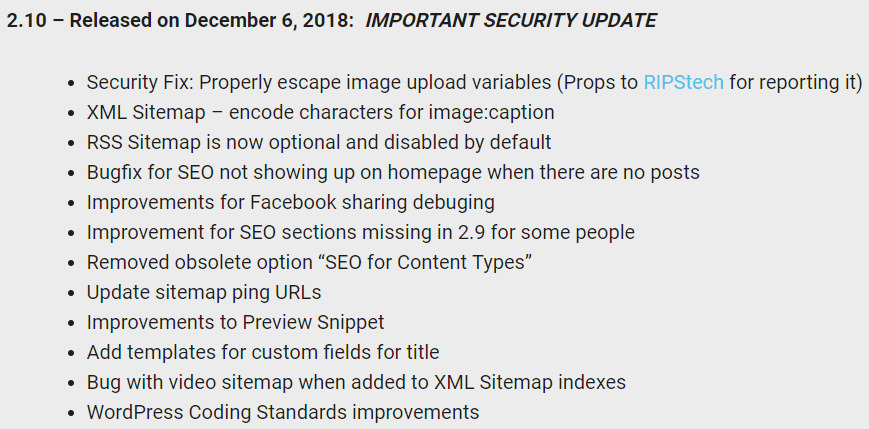 Screenshot of the changelog, altered after this article was published, to show that a patch was published.
Screenshot of the changelog, altered after this article was published, to show that a patch was published.As you can see, that new changelog is more upfront about the security patch than the original changelog, reproduced below:
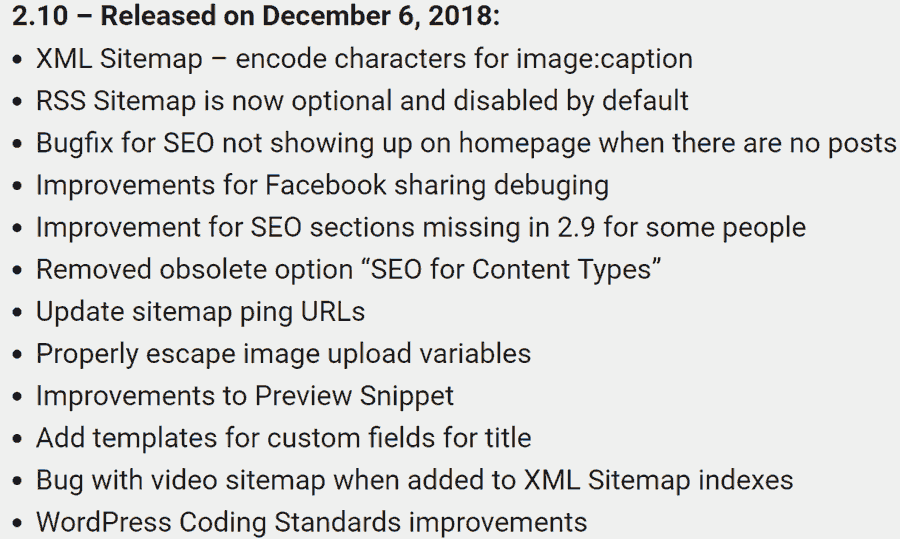 The All in One SEO Pack changelog at the time this article was written on December 11, 2018. This original changelog does not indicate that a security patch was issued for the XSS vulnerability.
The All in One SEO Pack changelog at the time this article was written on December 11, 2018. This original changelog does not indicate that a security patch was issued for the XSS vulnerability.The December 6, 2018 Changelog Did Not Show a Vulnerability Patch as of December 11, 2018
A changelog is a record of the changes made to a software at the time of a specific update. When All in One SEO Pack updated their software on December 6, 2018, there was no mention of a vulnerability patch, as can be seen in the screenshot above of the changelog at the time this article was written.
Only All in One SEO Pack can explain why the vulnerability patch was not mentioned. For all we know, someone forgot to mention it to whoever wrote the changelog and it was an innocent mistake and not an attempt to keep the vulnerability from being publicized.
I gave the plugin publisher the benefit of the doubt that they mistakenly omitted mentioning the vulnerability in the changelog. This article correctly reported that it was unknown if the plugin was patched.
It’s a fact that the vulnerability patch was not mentioned in the All in One SEO Pack changelog at the time the article was written.
It is a fact that the article correctly noted that it was not known whether the plugin was patched, based on the changelog that All in One SEO Pack themselves published.
Cross-Site Scripting Vulnerability
A cross-site scripting vulnerability (XSS) is a type of vulnerability that allows an attacker to insert a code into a web page. The code compromises the web page and allows the attacker to gain various levels of access to the website and/or website database.
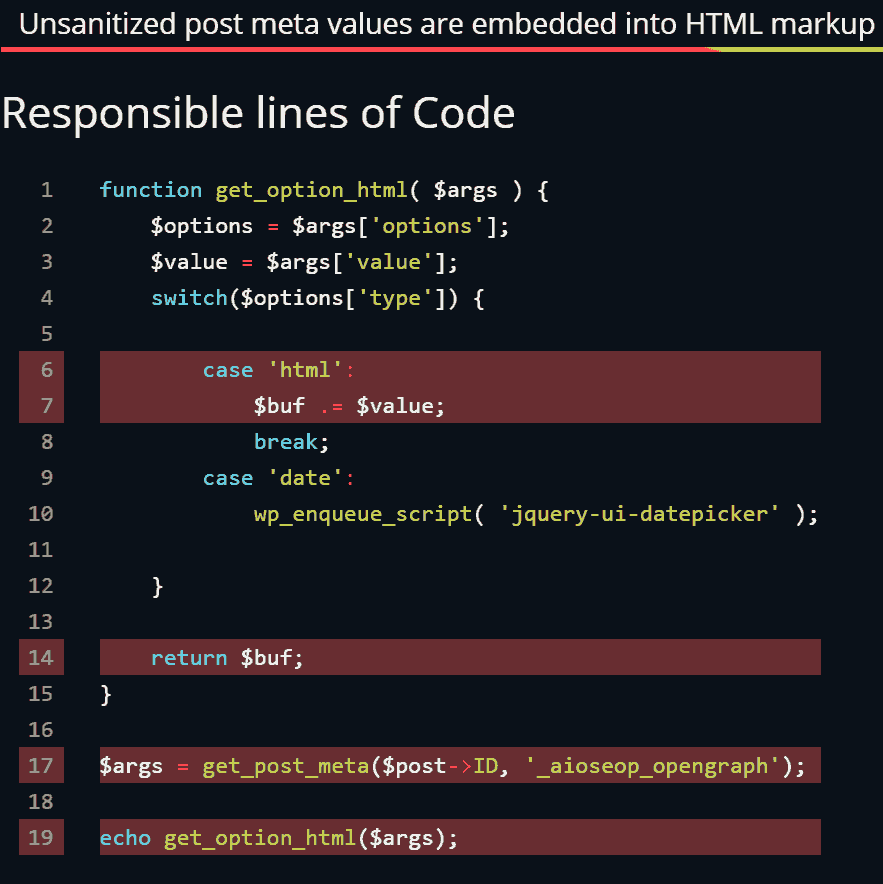 This is a screenshot from the RipsTech.com website showing the lines of code that contain the vulnerability.
This is a screenshot from the RipsTech.com website showing the lines of code that contain the vulnerability.Who Does the All in One SEO Pack Vulnerability Affect?
The All in One SEO Pack vulnerability affects websites that have at least a contributor level access enabled. The attacker must first gain access to at least the contributor level account in order to proceed with the XSS attack. It may be useful to make sure all user passwords from contributor level on up are secure.
How Does the Vulnerability Work?
Once an attacker has access to at least a contributor level user account, they can insert scripts into posts that then perform a variety of actions that can further compromise the website.
This is how the RipsTech site describes the vulnerability:
“An attacker is able to inject arbitrary JavaScript code into blog posts he creates and publishes. If an administrator opens a malicious blog post, evil JavaScript code executes which compromises the target server.”
Is there a Patch for the Vulnerability?
Updated:
At the time this article was published, All in One SEO Pack did not mention in their changelog that a security update was issued. Only after this article was published did they alter the changelog to show that a security patch was issued. Thus, now that All in One SEO Pack has updated their changelog, we can now confidently say that yes, a patch for the vulnerability has been issued.
A patch is an update to software that closes a vulnerability. When a WordPress plugin fixes a vulnerability, they issue a patch and note it in what’s called a changelog.
A changelog is a log of all the changes contained in a WordPress Plugin update. It’s a good idea to review the changelog before updating because it sometimes contains important information.
For example, some plugin authors will try to minimize that a plugin contains a vulnerability and will not formally communicate to their users how urgent it is to update the plugin. Some plugin authors will only make a reference to a “security fix” within their changelog.
That said, many plugin authors include an explanation. So it’s good to read the changelog to understand what’s being changed.
According to the RipsTech security software company, All in One SEO Pack have not responded to affirm that a patch has been issued.
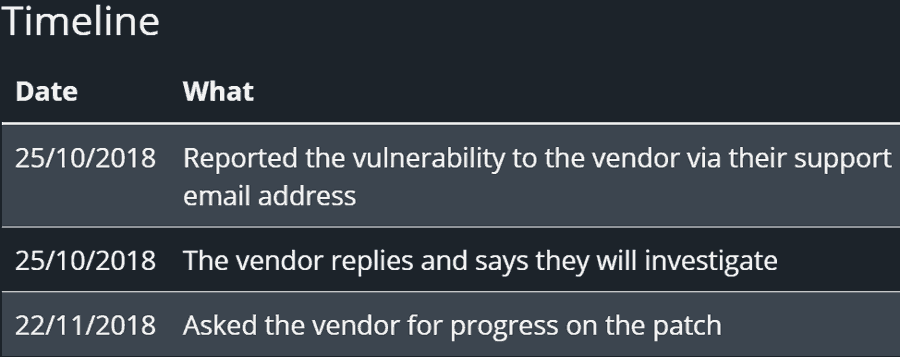
RipsTech reports that the vendor replied on October 25, 2018 that they will investigate the vulnerability. Almost a month later, on November 22, 2018, the security company contacted the vendor again. According to RipsTech All in One SEO Pack did not send a reply. Here is a screenshot of RipsTech timeline report:
All in One SEO Pack hosts a changelog on their website here.
According to All in One SEO Pack’s changelog as published on December 11, 2018, there have been no security updates. Screenshot is below:
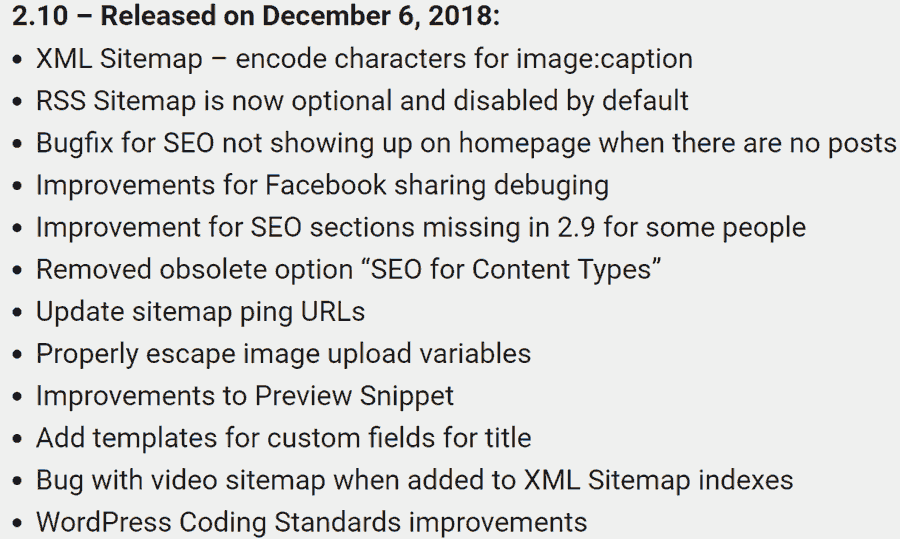 This is a screenshot of the changelog as of December 11, 2018, the date this article was written. It clearly shows that All in One SEO Pack did not indicate that a security patch was issued for the XSS vulnerability. There is zero mention of a patch.
This is a screenshot of the changelog as of December 11, 2018, the date this article was written. It clearly shows that All in One SEO Pack did not indicate that a security patch was issued for the XSS vulnerability. There is zero mention of a patch.UPDATED
After this article was published, the All in One SEO Pack changelog was altered to show that a patch for the vulnerability was issued. Here is a screenshot of the new changelog:
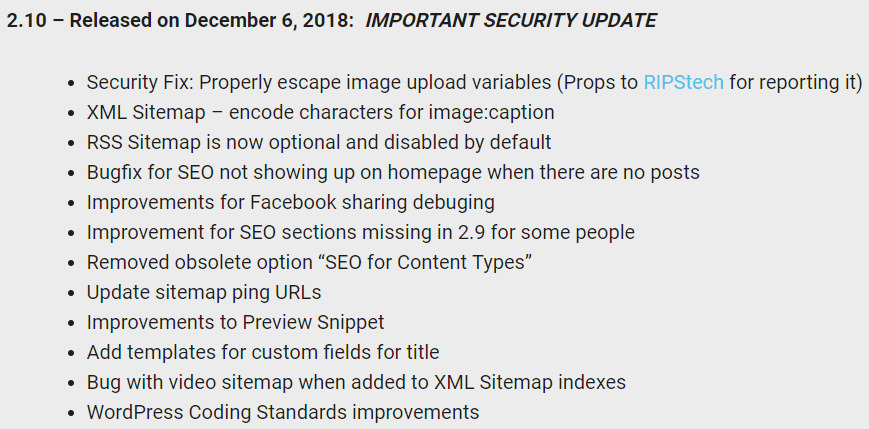 Screenshot of the changelog, altered after this article was published, to show that a patch was published.
Screenshot of the changelog, altered after this article was published, to show that a patch was published.
What Should You Do?
Updated:
Make sure your All in One SEO Pack is updated to the latest version. After this article was published, All in One SEO Pack updated their changelog to indicate that a vulnerability patch was issued on December 6, 2018.
In order for an attacker to exploit this vulnerability they would have to take control of a user account with at least the minimum level of contributor.
So it may be useful to tighten up all passwords to make sure none can be easily guessed. That will help prevent a hacker from guessing a password.
If you are not already using a WordPress security plugin like Sucuri Security or WordFence, you may wish to consider using one. These kinds of security plugins can slow down password guessing hack attacks.
View the original announcement at RipsTech:
Click the link below to visit their “Security Calendar” then click on the number 4 in the top row. That will spawn a pop up with all the details.
https://www.ripstech.com/php-security-calendar-2018/
Read the announcement at the WPScan Vulnerability Database
https://wpvulndb.com/vulnerabilities/9159
More Resources
- Yoast SEO 9.1 Vulnerability Explained
- Study Shows Web Security Directly Affects SEO
- Top 10 WordPress SEO Mistakes to Avoid
- 10 Awesome WordPress SEO Plugins to Optimize Your Site
Images by Shutterstock, Modified by Author
Screenshots by Author, Modified by Author