One of SEO’s hottest topics recently has been the need to migrate from HTTP to HTTPS, especially for those websites which collect personal data or passwords. Websites serving content over the secure HTTPS protocol have been given a ranking boost since 2014. Google Chrome (which owns ~55% of the desktop browser market) is visibly branding websites as secure.
In Google Chrome 56, the upcoming browser update will also start branding websites served on HTTP as not secure. (If you haven’t yet made the switch to HTTPS, you should read this SEJ article from Tony Messer.)
So what’s next on Google’s agenda? Within the SEO community, we already know that Google is able to ‘guess’ standard URLs on websites, such as XML sitemaps, about pages, and contact pages. Could it be plausible for Google to start making passive scans of websites too?
Passive scanning is a form of web vulnerability testing and is seen as a less dangerous alternative to active vulnerability testing, where a system is probed and stressed, and carries risks ranging from performance lag to system crash.
While passive scans won’t discover as much as an active test, they may provide enough information to aid an IDT (Intrusion Detection Tool).
The Case for Google and Passive Scans
As HTTPS becomes widespread and the new standard for all websites, the bar of what is and isn’t safe needs to be raised again.
At the end of 2016, Google Webmasters published a link to the Sucuri 2016/Q2 Hacked Website Report, highlighting analysis of 9,000 infected websites made up of WordPress, Joomla!, Magento, and Drupal builds.
Google’s main reason for flagging this report is the increased number of hacks for SEO purposes. Hackers targeted search optimized websites to ‘piggyback’ off of their good rankings. After gaining access, they created malicious 301 redirects to other websites. The intention is to extract information or money from the user, or infect their machine with malware, ransomware, or viruses.
A site hack can leave lasting damage. For example, the below screenshot is of my landlord’s website:
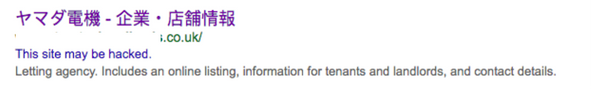
This is a WordPress website that was hacked via an outdated plugin. Instead of displaying a title tag for a letting (leasing) agency based in the North of England, it’s displaying the name of a Japanese consumer electronics company.
The website still appears within Google UK for its exact match name, but little else. Anyone who comes across the site via online search will likely perceive this as a black mark against my landlord’s trust and credibility.
Secure Your Website Ahead of Time
Google has given us warning that they are going to start marking websites as unsecure in Chrome 56, giving webmasters the opportunity to migrate to HTTPS. But there is currently no indication that there will be any advance notice of passive scans or other security checks. Here’s how you can stay ahead of the game:
- If you’re running open source software, it’s important that you keep it up-to-date and ensure it’s updated to the latest version.
- Check your plugins. According to the Sucuri report, 22% of all WordPress hacks they found came from three plugins not being updated. It’s estimated that WordPress websites have an average of 12 plugins installed. Any that haven’t been updated recently by the developer should be considered for replacement. Plugins that have been abandoned by developers can become unsecure over time and offer easy access to a website.
- Use an edge network company and put your website behind a Web Application Firewall (WAF) such as Cloudflare or Amazon AWS. This will protect your website from a number of online attack types such as SQL injections or cross-site scripting.
- Note that Google could also include known vulnerabilities that aren’t platform-specific in their passive scans, such as the OWASP Top 10. The OWASP updates each year and identifies the top 10 flaws that are being exploited by hackers. You should stay on top of their recommendations and updates.

How Do I Know If I’ve Been Hacked?
There are a number of articles and studies that claim that the ‘This site may be hacked’ message only appears on 50% of all websites that have been hacked. While Google now says they will flag malicious redirects they identify via Google Search Console, you still can’t rely on Google as your only indicator as to whether your site has been compromised.
In my experience, keeping an eye on your Search Console data for anomalies is worthwhile. In one case, I saw a non-sports related site start to inexplicably gain impressions for cheap NFL jerseys and sportswear terms. This turned out to be “bait & switch” hacking: the hackers had managed to inject around 500 sportswear-related pages, and all redirected to another website via JavaScript. What did the hackers gain from all this? An affiliate fee from the click.
Lastly, if you’re seeing an unexplained drop in traffic or rankings, hacking should be considered (as one of many possibilities).
Putting the User First
Google has been both reactive and proactive to the change in search behavior, as users move to spend more time on mobile vs desktop.
Given that their Webmaster’s blog post also promotes the vision of a no hack web (sporting the #NoHack hashtag), in my opinion there is a strong case for Google incorporating both passive scans and/or ranking incentives for websites that are secure beyond HTTPS encryption. Google already takes into account whether or not a website affects “your money or your life” (YMYL), so passive scans could be an extension of this philosophy, as a hacked website could obviously impact a user in profoundly negative ways.
Image Credits
Featured Image: Image from Unsplash
In-post Photos: Images from Pixabay and self-taken screenshots


