Popular WordPress Plugin Popup Builder was discovered to have multiple vulnerabilities. These vulnerabilities could allow an attacker to inject malicious JavaScript into a popup.
Vulnerability in Popup Builder Plugin Discovered
The vulnerability was discovered by WordFence on March 4, 2020 and subsequently contacted the developers. The WordPress plugin vulnerability affects Popup Builder versions that are less than version 3.64.1.
The plugin developers uploaded a patched file a week later on March 11, when the updated plugin was made available for download.
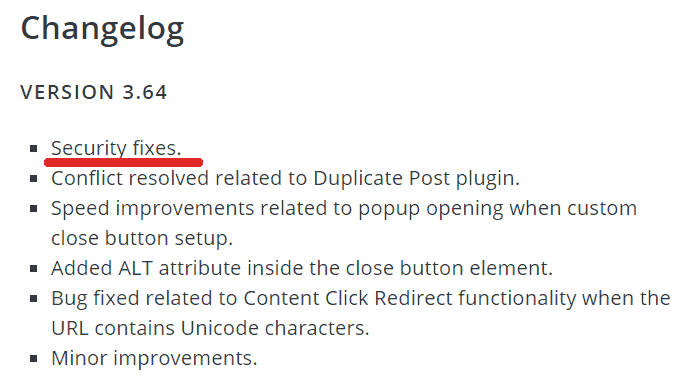
Changelog
A changelog is an explanation of what an update is about. It’s important for a changelog to be descriptive so that the plugin user can know that something is urgent.
Unfortunately, some WordPress plugin developers either don’t mention the security issue or describe it in vague and generic terms.
Popup Builder plugin’s changelog notes that there is a security update but it doesn’t mention the severity or importance of it. It’s vague but at least they disclose that the update addresses a security concern.
The update is described as “Security fixes” which technically communicates that a security issue has been patched but doesn’t provide a sense of urgency necessary for a vulnerability of this seriousness.
Here is a screenshot of Popup Builder’s changelog:
What are the Vulnerabilities?
There are two vulnerabilities. The first vulnerability allows someone to insert harmful JavaScript into a popup.
The second vulnerability allows the attacker to download subscriber lists and gain access to numerous plugin features.
This vulnerability affects over 100,000 plugin users. It’s important for publishers to download and update their plugins.
According to security plugin maker Wordfence:
“Typically, attackers use a vulnerability like this to redirect site visitors to malvertising sites or steal sensitive information from their browsers, though it could also be used for site takeover if an administrator visited or previewed a page containing the infected popup while logged in.”
It’s very important to update this plugin. Failure to do so could invite hackers to take over a site.
Read the announcement by WordFence:
Vulnerabilities Patched in Popup Builder Plugin Affecting over 100,000 Sites